Imagine a world without technology, a computer that helps us in our office works and solutions, a cellphone that aids us in communicating with our loved ones even abroad, without Television and radio that entertains us every night, without a car that conveys us from places, and even without internet that almost everyone needs. The feeling is like dark age, a generation with a simple tool used in solving a complex problem. Thanks to Information technology, we did not have that kind of feeling.
Per definition from techtarget.com, “Information technology (IT) is the use of any computers, storage, networking and other physical devices, infrastructure and processes to create, process, store, secure and exchange all forms of electronic data.” IT on what we have discussed is also interchangeable with Information System where it defines as the combination of hardware, software, network, procedures and the people.
In almost all aspect of our daily lives, we use IT tools, gadgets and devices. This paved way for us to become effective and efficient in our workplace and in personal doings. But does IT really matter? Yes IT does. For an organization, neglect of IT is like neglecting a gold in the mine, not maximizing the benefits and opportunities of it.
Despite the increasing trend of the outsourcing, keeping an in-house IT personnel and department is also necessary, this does not mean that the organization is outsourcing its IT services, they will dispose it. The IT department will keep and maintain the IT assets and services and will also translate business objectives and strategies into IT language and strategies also.
Business nowadays also are inclined with business ideas through disruptive technological campaigns, case and point is how Uber and Grab are marketed, in which they disrupt the normal idea of having to commute and public transport; also the case of Facebook to keeping updated and connected with your friends and relatives.

Not maximizing the benefits of IT will surely leave the organization with nothing, just like what happened with Kodak where they did not innovate and fully use the benefits of technology, thus they had overtaken by competitors who developed a digital cameras from analog cameras that use films.
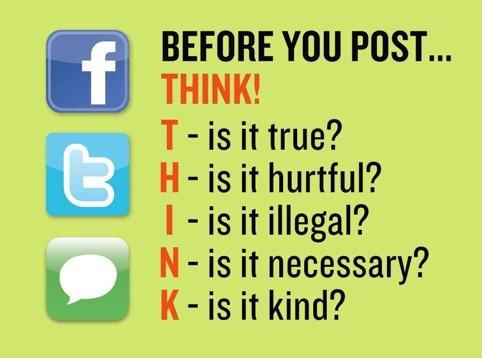
On a more personal note, does IT matters to me? Yes IT does. IT helped me established good connections and relationships with people through social media. Keeping and staying connected with my loved ones is never been easier with the present technology also. When you’re alone, family, relatives and friends can instantly be reached upon virtually, sometimes keeping my sanity in a solitary moment.

Staying upbeat professionally has never been easier without the use of IT also. Collaboration tools made the life at work easier since us employees can collaborate on a project faster and easier. Computing tools such as MS Excel has also helped me compute data and information easily and also transform a raw data into a meaningful information such as from daily sales invoice of a distributor, to the top selling sku per month per customer etc.

In the end, as the technology grows, individuals and organizations must stay afloat in the flowing advancement of technology, to create, develop, maintain, check cycle of an innovation.
References:










 “The Key to success in any organization is identifying, developing, and empowering the right people” – Craig Groeschel
“The Key to success in any organization is identifying, developing, and empowering the right people” – Craig Groeschel